If you’re a C2 customer or have followed the Arctic Wolf cybersecurity journey, you’ll know that we believe cybersecurity has an effectiveness problem.
Every year new technologies, vendors, and solutions emerge claiming to be the final piece of the puzzle. Yet, despite this constant innovation, we continue to see high-profile breaches in the headlines. All organizations know they need better security, but the dizzying array of tools leaves resource-constrained IT and security leaders wondering how to proceed.
We also believe that solving this problem does not mean adding more tools to the environment. That just adds complexity, more alerts, and frustration for fatigued IT and security teams. Solving this challenge requires a focus on security operations.
It’s also why we’re sharing the first-ever Arctic Wolf Security Operations Report.
Leveraging insight from experiences, this report highlights security trends that the Arctic Wolf security operations team is seeing, along with advice on how to advance your own security operations capabilities.
It reveals, that despite the number of publicly disclosed data breaches being down year over year, the amount of corporate credentials with plaintext passwords exposed on the dark web has increased by 429 percent since March. For a typical organization, this means there are now on average 17 sets of corporate credentials available on the dark web for hackers to execute credential stuffing and brute-force attacks against.
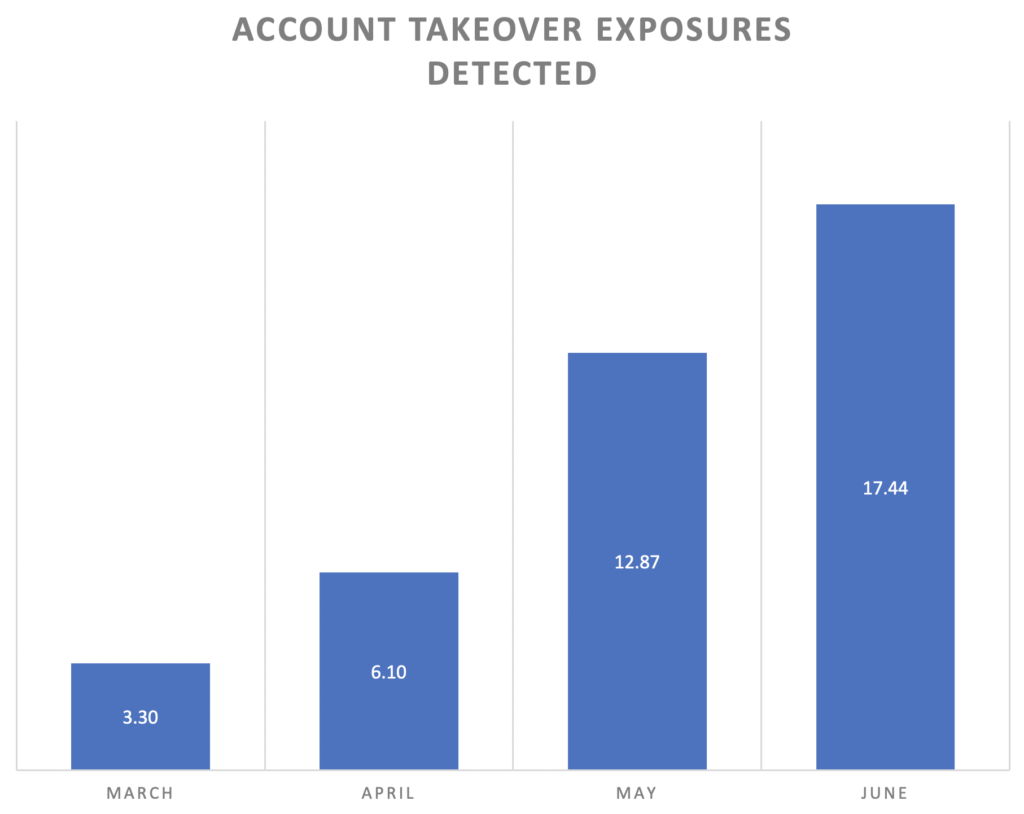
Figure 1: Average number of account takeover exposures per customer, per month (March-June)
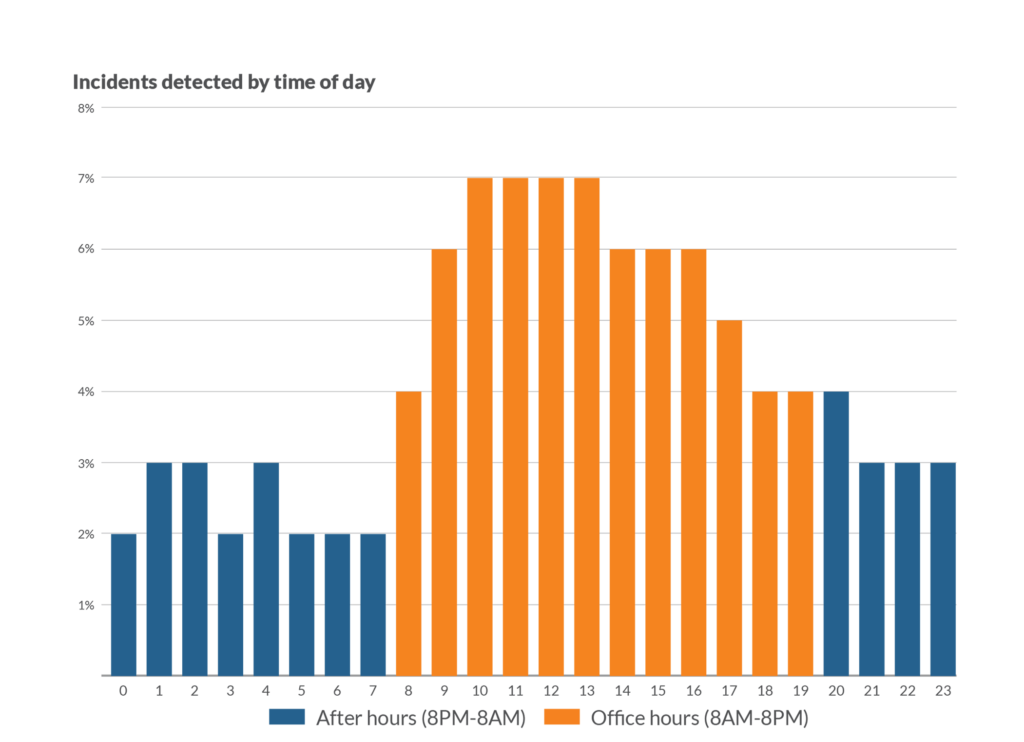
This sharp increase in corporate credential leaks underscores the need for organizations to have dedicated 24×7 monitoring of their network, endpoint, and cloud environments. Of all of the high-risk security incidents observed by Arctic Wolf, the report also reveals that 35% occur between the hours of 8:00 PM and 8:00 AM, and 14% occur on weekends; times when most employees and contractors are not online.
The Arctic Wolf Security Operations Report also provides insight on how COVID-19 has increased the number of security operations challenges facing organizations, some of which include:
- A 64 percent increase in phishing and ransomware attempts – Hackers have created new phishing lures around COVID-19 topics and modified traditional lures seeking to take advantage of remote workers.
- Critical vulnerability (CVE) patch time has increased by 40 days – A combination of higher CVE volumes, more critical CVEs, and the emergence of a remote workforce has significantly slowed down the patching programs many organizations.
- Connections to open and unsecured WIFI networks is up by over 240 percent – Remote workforces connecting to open and unsecured WiFi networks outside of the office or home are now facing increased risks of malware exposure, credential theft, and browser session hijacking.
The pandemic completely changed the target environment and impacted people responsible for protecting it, but if you embrace security operations your business is more secure, more resilient, and better able to adapt.
Get started today and contact a cybersecurity specialist at C2.
